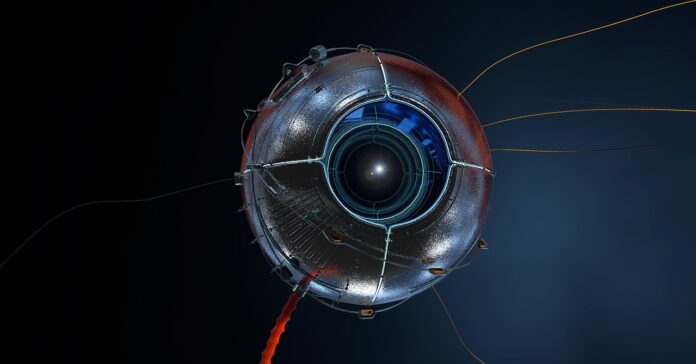
The widespread use of an automotive monitoring device manufactured in China poses a significant threat of cyberattacks, according to specialists in the field of information security.
An attack on or through a computer network is known as a cyberattack. Cyber attacks are attacks by criminals using computers to inflict damage on one or more systems and networks. Computers can be purposefully disabled, data can be stolen, or a penetrated computer can be used as a starting point for subsequent attacks in a cyber attack. Malware, phishing, ransomware, and denial-of-service attacks are just a few of the many tools that cybercriminals employ in their attacks.
People worldwide use the device to prevent their automobiles from being stolen. The product is made by MiCODUS, which has its headquarters in Shenzen.
A report compiled by the cybersecurity company BitSight, based in the United States, has warned that the system contains significant software vulnerabilities.
According to the security researchers’ findings, the vulnerabilities could make it possible for adversaries to hijack automobiles remotely by employing the tracking device. According to the analysis published by BitSight, this could allow attackers to turn off the gasoline supply or take control of the car while it is in motion.
According to BitSight, the MV720 device may be purchased for less than $25. The researchers have just now published a press statement in which they strongly recommend that all device users immediately stop using it until a patch is made available to address the vulnerabilities.
The research by BitSight was published at the same time as an official advisory issued by a government body in the United States, which also identified the device’s weaknesses.
BitSight disclosed to the Associated Press that it had been attempting to contact officials of MiCODUS since September to have a conversation about the security vulnerabilities it had discovered. It reported that those efforts had not been successful. BitSight stated that the Cybersecurity and Infrastructure Security Organization (CISA), the agency in the United States examining the device, joined its efforts to interact with MiCODUS in April.
The Associated Press reportedly sent an email to MiCODUS regarding the issue; however, the news organization did not receive a response.
The CISA issued a statement claiming that it was unaware of “any active exploitation” of the vulnerabilities.
Vehicle groupings, including trucks, school buses, and even military vehicles, can be tracked using GPS trackers, which are utilized worldwide. The devices also provide security for the cars, so they are not misplaced or stolen.
In addition to gathering information on the location of vehicles, many devices also can analyze additional data about the operation of vehicles and their drivers. This information can include the driver’s driving habits and fuel use. A good number of gadgets can control a car’s fuel or locking systems and other functions.
According to BitSight, a cyber attacker might remotely disconnect the gasoline line of a moving car by using the MV720 gadget. According to Pedro Umbelino, a researcher at BitSight, an attacker would also be able to see where a vehicle is located in real-time to spy on it.
BitSight discovered that more than ninety percent of users do not change the device’s factory-default password, which is one of the most severe security flaws associated with the device. Additionally, it found vulnerabilities in the web server’s software to operate the machines over the internet.
According to MiCODUS, around 1.5 million gadgets have been sold and utilized by 420,000 customers.
According to the findings of BitSight’s research, the company’s clients include a large energy company, an aerospace company, and a national military in South America and Eastern Europe. Among the others were a federal law enforcement agency in Western Europe and a company that operated a nuclear power plant. BitSight did not identify any of the businesses in question. Brazil, Mexico, Spain, and Russia were among the countries with the highest users.
Richard Clarke is a former senior officer in charge of cybersecurity for the United States. In an interview with the Associated Press, he stated that even though he does not believe the gadget was planned to be “used maliciously by the Chinese government,” there is still the risk.
According to Clarke, the threat is quite natural because Chinese businesses are legally obligated to carry out the directives of their government. “You simply have to ask, how frequently are we going to find these things that are infrastructural – where there’s the possibility for Chinese abuse – and the users don’t know?” Clarke stated.